Archive for Information technology
July 7, 2025 @ 10:17 am· Filed by Victor Mair under Bibliography, Books, Information technology
[Posted with the permission of the author, David Helliwell]
Almost exactly five years ago, I was dismissed on the grounds of age from my post as Curator of Chinese Collections at the Bodleian Library. I had been in office for over 41 years. The last six of those were particularly pleasurable as I was able to spend all my time organising, identifying, and cataloguing the Library’s “special collections” of Chinese books. Meanwhile, Joshua, who had been appointed to take over all my other duties, did all the hard work.
My teenage years were spent in the 1960s, and we children of the sixties, as demonstrated so well by Paul McCartney at Glastonbury this year, never grow old. We simply become less young. We also have the advantage of being able to recall what to many, if not to most colleagues in this room, is the distant past.
Read the rest of this entry »
Permalink
March 19, 2025 @ 5:11 am· Filed by Victor Mair under Artificial intelligence, Bibliography, Etymology, Information technology, Translation
The words that leap to mind are pustakālaya पुस्तकालय (pustak पुस्तक ["book"] + ālaya आलय ["place"]) and granthālaya ग्रन्थालय (granth ग्रंथ ["text"] + ālaya आलय ["place"]). Those are simple and straightforward.
There were several other Sanskrit words for library I used to know, such as vidyākośasamāśraya विद्याकोशसमाश्रय* that included the component vidya ("knowledge"), but they were more subtle and complicated, so they were harder for me to recall.
*knowledge treasury coming together (for support or shelter)
Read the rest of this entry »
Permalink
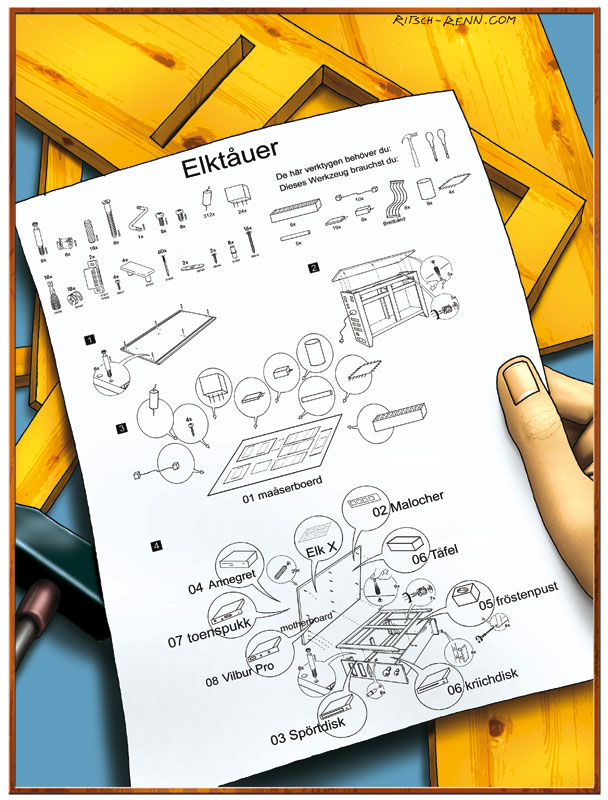
March 11, 2025 @ 11:50 am· Filed by Victor Mair under Information technology, Language and art
Some assembly required.
From Olaf Zimmermann:
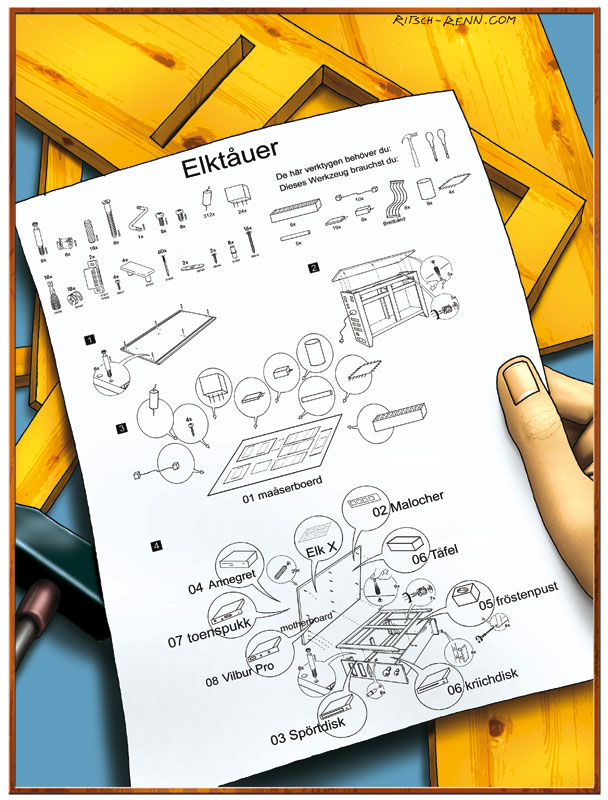
(source [2002 no. 5])
Read the rest of this entry »
Permalink
March 8, 2025 @ 12:12 pm· Filed by Victor Mair under Information technology, Language and business, Language and culture, Language and fashion
First, how to say the name.
I think that the "correct" pronunciation of IKEA is "ee-kay-uh", with emphasis on the "ee" sound, similar to the way a native Swedish speaker would say it, not "eye-kee-ah" or "ai-kee-uh" with stress on the second syllable, the way most Americans say it (all the Americans I know).
What does it mean?
IKEA is an acronym for Ingvar Kamprad Elmtaryd Agunnaryd, the names of the founder and the places where he grew up.
Read the rest of this entry »
Permalink
February 4, 2025 @ 11:00 am· Filed by Victor Mair under Classification, Information technology, Language and music, Language and science, Languages, Names, Topolects
[This is a guest post by Conal Boyce]
Overview: Here we look at some technical terms and how they’ve fared since their release to, or adoption by, the public: information theory; (TW) the colored quarks of Nambu and Han; cosmic‑ray decay according to Millikan; the Sinitic languages (Mair) vs. ‘the Chinese language’ (misnomer); Wu’s cosmic chirality as the violation of a nonNoetherian principle.
① information theory is the mother of all factoids. Why would one call it that? Because there is no such thing, only the following phantom utterance that is ubiquitous: “Shannon’s information theory.” In 1948, Shannon wrote a paper on the mathematics of data‑communication technology, and named it accordingly. Put off by its name, science journalists introduced it to the world as “information theory.” The name stuck, suggesting in the minds of innocents something so deep and epochal that it might even shed light on Mozart. Shannon 1948 is the big example of how of data and information have been confounded for 3/4 of a century, but it is accompanied by innumerable smaller cases, as when Susskind argues that “in physics we treat them as pretty much the same thing” (paraphrase; details in Appendix A). Here is a rough‑and‑ready demonstration of how different they actually are: “Go.” ←That’s just data, but place it in a context, and a layer of information now “rides on it” (or floats above it, on a different plane) such that this is conveyed: “Go to the store now before it closes”; or this: “Fly now to Hiroshima and drop the bomb.” True, in shop‑talk and hallway conversations, a database developer or data‑comm engineer might toss the terms data and information around as if one believed them to be interchangeable. Then, overheard by someone in the world at large, such casual usage is easily misconstrued, leading astrophysicists to fret in public over the “information” that might be “lost” in a black hole. (As for an actual Theory of Information, we must wait for a superintelligent computer to produce it since that task is far beyond human ability. And once coughed up, it will be so lengthy as to require several lifetimes to read it, and in any case, largely incomprehensible to us.)
Read the rest of this entry »
Permalink
July 31, 2024 @ 2:50 pm· Filed by Victor Mair under Censorship, Information technology
By now, we've had dozens of posts about the Great Firewall, VPNs, internet censorship, and so forth, but they're all from the vantage of the outside trying to look in. Of course, that gives us a skewed picture of what the situation is really like with regard to the internet inside and outside of the PRC. This is not a healthy situation, for nearly one fifth of the world's population (17.72%) live inside the borders of China. To be ignorant of how they are living is dangerous, for we may make erroneous assumptions about what one fifth of humanity is doing and thinking.
Fortunately, at last I have found an American expat who has been living and working in the PRC for more than a decade at a remote location and is well connected with many Chinese colleagues. He is an active scholar and very well informed about the internet, AI, databases, and so forth, both inside and outside of the PRC. I should note that he does not live among expats. In fact, he is the only Westerner where he is located, quite far from major metropolitan areas, so he truly understands what Chinese of all walks of life do on a day-to-day basis.
Read the rest of this entry »
Permalink
June 10, 2024 @ 8:56 am· Filed by Victor Mair under Censorship, Information technology, Language and computers, Language and politics
Things are becoming dicey for the CCP/PRC regime:
"A cartoon cat has been vexing China’s censors – now he says they are on his tail"
By Tessa Wong, Asia Digital Reporter, BBC (6/10/24)
Here's the dilemma faced by the Chinese communist authorities. It would be very easy for the censors to shut down all VPNs and invoke strictly draconian internet controls that would make it impossible for netizens to communicate with the outside internet. But that would mean that China would no longer have access to external information and communication, which the government desperately needs if they are going to continue to acquire advanced technology and science from abroad, not to mention operate their economic initiatives such as BRI (Belt and Road Initiative).
Read the rest of this entry »
Permalink
May 30, 2024 @ 10:46 am· Filed by Victor Mair under Information technology, Language and computers
Both for the flow of and access to information.
More than a week ago, the Seattle Public Library system, a large and wonderful institution that thousands rely on every day, went offline after ransomware hackers attacked it.
"Why did ransomware hackers target Seattle Public Library?", GeekWire, by Taylor Soper (May 29, 2024)
This is an excellent article that explains why the criminals went after a library, how they carried out their dirty work, and what the authorities are doing to restore services.
Read the rest of this entry »
Permalink
October 29, 2023 @ 3:35 pm· Filed by Victor Mair under Information technology, Neologisms
Placed on the countertop of the coffee corner in the dining hall at Lingnan University in Hong Kong:

Read the rest of this entry »
Permalink
September 13, 2023 @ 5:41 am· Filed by Victor Mair under Artificial intelligence, Information technology, Language teaching and learning, Writing
This is a problem that has been troubling colleagues across the country.
"Why fewer university students are studying Mandarin"
Learning the difficult language does not seem as worthwhile as it once did
Economist (Aug 24th 2023)
China | How do you say “not interested”?
Ten years ago Mandarin, the mother tongue of most Chinese, was being hyped as the language of the future. In 2015 the administration of Barack Obama called for 1m primary- and secondary-school students in America to learn it by 2020. In 2016 Britain followed suit, encouraging kids to study “one of the most important languages for the UK’s future prosperity”. Elsewhere, too, there seemed to be a growing interest in Mandarin, as China’s influence and economic heft increased. So why, a decade later, does Mandarin-learning appear to have declined in many places?
Read the rest of this entry »
Permalink
April 15, 2023 @ 6:27 am· Filed by Victor Mair under Data bases, Information technology, Language and art, Language and philosophy, Language play, Linguistics in the comics, Logic, Memes
From Phillip Remaker:
Loved your deep dive on finding the provenance of the "conspiracy theory" image.
The one that claimed authorship clipped the edge of the unicorn tail.
The only version I have found that doesn't clip the edge of the unicorn tail is
this one from
farhan
I don't know if that means I found the original or if the author touched it up. The page is not archived on the Internet Archive.
It seems consistent with his other art.
Read the rest of this entry »
Permalink
September 7, 2022 @ 8:33 pm· Filed by Victor Mair under Information technology, Language and computers, Language and literature, Philology
Just out today, this is one of the longest book reviews I have ever written:
Jack W. Chen, Anatoly Detwyler, Xiao Liu, Christopher M. B. Nugent, and Bruce Rusk, eds., Literary Information in China: A History (New York: Columbia University Press, 2021).
Reviewed by Victor H. Mair
MCLC Resource Center Publication (Copyright September, 2022)
I am calling it to your attention because the book under review, which I will refer to here as LIIC, signals a sea change in:
1. Sinology
2. Information technology
3. Academic attitudes toward the study of language and literature
Read the rest of this entry »
Permalink
July 10, 2022 @ 4:41 am· Filed by Victor Mair under Diglossia and digraphia, Emojis and emoticons, Information technology, Language and computers, Language teaching and learning, Typing, Writing systems
[This is a guest post by Paul Shore.]
The 2022 book Kingdom of Characters by Yale professor Jing Tsu is currently #51,777 in Amazon's sales ranking. (The label "Best Seller" on the Amazon search-results listing for it incorporates the amusing mouseover qualification "in [the subject of] Unicode Encoding Standard".) I haven't read the book yet: the Arlington, Virginia library system's four copies have a wait list, and so I have a used copy coming to me in the mail. What I have experienced, though, is a fifty-minute National Public Radio program from their podcast / broadcast series Throughline, entitled "The Characters That Built China", that's a partial summary of the material in the book, a summary that was made with major cooperation from Jing Tsu herself, with numerous recorded remarks by her alternating with remarks by the two hosts: https://www.npr.org/podcasts/510333/throughline (scroll down to the May 26th episode). Based on what's conveyed in this podcast / broadcast episode, I think many people on Language Log and elsewhere who care about fostering a proper understanding of human language among the general public might agree that that ranking of 51,777 is still several million too high. But while the influence of the book's ill-informed, misleading statements about language was until a few days ago mostly confined to those individuals who'd taken the trouble to get hold of a copy of the book or had taken the trouble to listen to the Throughline episode as a podcast (it was presumably released as such on its official date of May 26th), with the recent broadcasting of the episode on NPR proper those nocive ideas have now been splashed out over the national airwaves. And since NPR listeners typically have their ears "open like a greedy shark, to catch the tunings of a voice [supposedly] divine" (Keats), this program seems likely to inflict an unusually high amount of damage on public knowledge of linguistics.
Read the rest of this entry »
Permalink